Cybersecurity is drawing interest, both as an going concern to protect technology from attacks and a growing industry in the region. It’s an area that’s gaining a foothold in the tech community and contributing to job growth.
Over the course of our reporting, we’ve found this field has some specific language that can be important when it comes to understanding where potential threats may lie, or what a company does.
So, as we focused on cybersecurity this month, we in D.C. and Baltimore decided to ask local leaders in the field about some of the terms we’ve been hearing — and one of those was “cybersecurity” itself. The following is a look at our first compilation of cybersecurity terms to know. It’s by no means a complete glossary (yet!), but consider it a snapshot of some of the key terms that often come up in conversation at networking events and interviews.
Here’s a look:
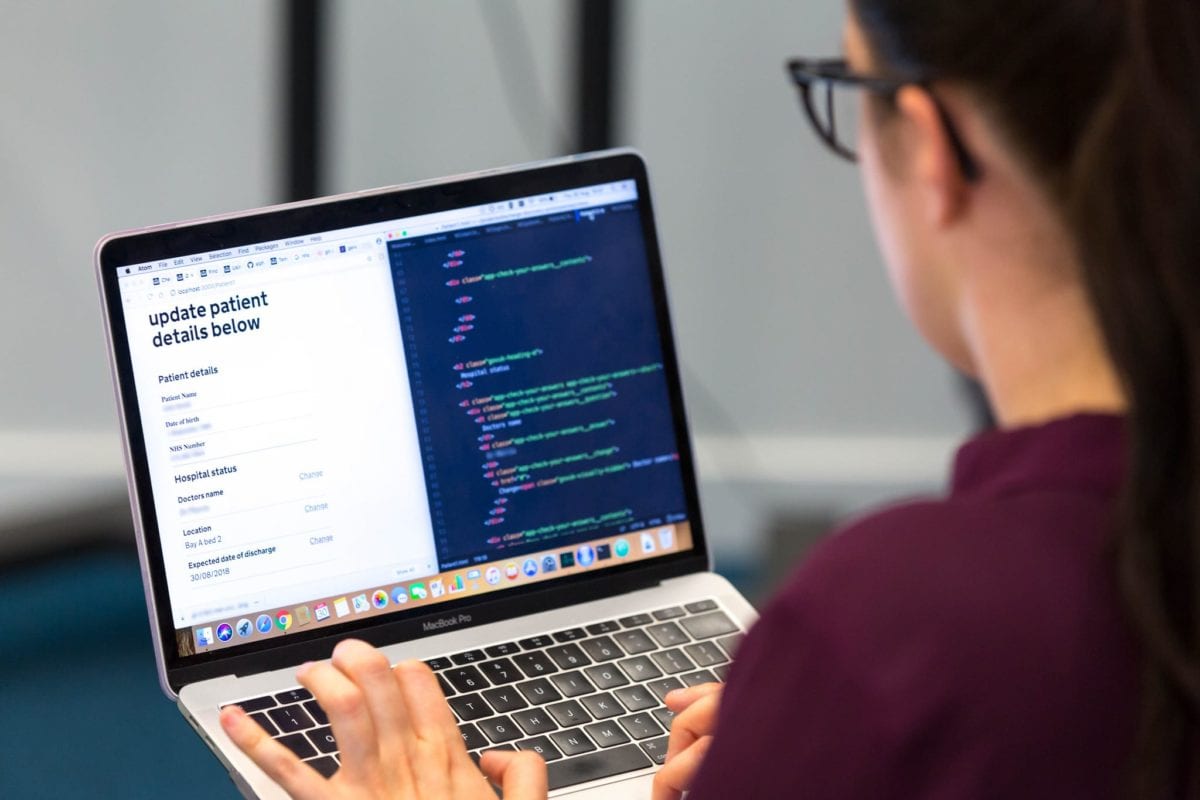
Application security
- “A process for enhancing the security posture of software. The process typically involves: threat modeling, design reviews, finding security bugs through tools/testing (IAST, RASP, SAST, DAST, manual, etc), and then fixing the security bugs in the software development lifecycle (SDL). Application security is being adapted in to more streamlined ‘DevSecOps’ processes in today’s development world.” — David Lindner, director of application security at Contrast Security
Cloud
- “Emerging technology that allows us to access our files and/or services through the internet from anywhere in the world. Technically speaking, it’s a collection of computers with large storage capabilities that remotely serve requests.” — Diego Salinas, assistant director of cybersecurity accelerator MACH37
Cyber exposure
- “An emerging discipline used to accurately understand and reduce cyber risk. This approach is key to helping companies safeguard valuable assets and become more cyber secure by providing holistic visibility into the various digital compute platforms and assets that make up the modern attack surface. The Cyber Exposure process takes the whole life cycle into account, allowing companies to determine where they are exposed, where they should prioritize based on risk and how they are reducing exposure over time.
A Cyber Exposure approach builds on the roots of vulnerability management for traditional IT systems, but also includes:
- Live discovery of every modern asset across any computing environment
- Continuous visibility into where an asset is secure, or exposed, and to what extent
- Added context to help prioritize and select the appropriate remediation technique
- A framework to accurately represent and communicate cyber risk to business
- Tools to apply Cyber Exposure data as a key risk metric for strategic decision support”
— Jill Shapiro, senior director of global government affairs at Tenable
Cybersecurity roadmap
- “A cybersecurity roadmap helps businesses align their planned cybersecurity investments with their future business goals. Once businesses know which security risks threaten their growth, they can make more strategic cybersecurity investments.” — Lauren Maffeo, GetApp
Data archiving
- “Data archiving involves storing historical data on a separate storage system. Data should be archived when it’s no longer being used, but must be saved for record-keeping and/or to maintain regulatory compliance.” — Maffeo
Endpoint
- “Endpoint refers to any device that connects to a network and can serve as an entry point for security threats. Devices such as smartphones, tablets and laptops are all endpoints that must be secured to block unauthorized access to company networks. Endpoint security also can prevent the internal theft of sensitive data.” — Leo Minegishi, director of information security, Summit Business Technologies
Firmware
- “A specific class of computer software, firmware provides the low-level control for the hardware of an IoT device.” — Terry Dunlap, cofounder and chief strategy officer, ReFirm Labs
IP Address
- “A unique series of numbers that identifies a device connected to the Internet or a local network. Allows systems to be recognized by other systems via Internet Protocol.” — Salinas
IoT Security
- “Internet of Things (IoT) security includes both the physical security of internet-connected devices and the network security to which each IoT ‘thing’ connects.” — Dunlap
Known exploits
- “Exploits are a program or piece of computer code that takes advantage of a security flaw in an application or system. Known exploits are exploits that have been identified, documented and publicly reported by security researchers.” —Dunlap
Malware
- “Malware, or malicious software, is any program or file that is written with the intent of doing harm to data, devices or to people. Common types of malware include computer viruses, Trojan horses and spyware.” — Dunlap
MSSP
- “MSSP stands for ‘managed security service providers.’ They provide outsourced monitoring and management of security devices and systems. MSSP can be outsourced or managed in-house. Services include firewall management, vulnerability scanning, and anti-viral protection.” — Maffeo
Phishing
- “Hackers use this technique to ‘trick’ people into giving them sensitive information. Can come as emails with sketchy links, or be websites that look legit but are fake sites to obtain your information.” — Salinas
Ransomware
- “A form of malware that infects your device and prevents or limits users from accessing their systems until a ‘ransom’ is paid.” — Salinas
Spear phishing
- “A technique used by attackers to obtain sensitive information. Traditionally executed using highly targeted email messages designed to trick people into divulging personal or confidential data.” — Paul Taylor, Point3 Security
Third-party risk
- “Third-Party Risk, or supply chain risk, is the probability of a cybersecurity event affecting your company that is caused by a third party, such as a vendor partner, supplier, or contractor with whom you do business. The greater the number of partners, the higher the risk.” — Mohamoud Jibrell, CEO, NormShield
Virtual private network
- “A tool that allows the user to remain anonymous while using the internet by masking the location and encrypting traffic.” — Salinas
Zero day exploits
- “A cyberattack on a software or hardware vulnerability before it can be detected and fixed. Attackers exploit the security flaw by releasing malware that can take control of your computer, steal your data, corrupt files, access your contacts, and send spam messages from your account.” — Leo Minegishi, director of information security, Summit Business Technologies
- Dunlap points out that these are also known as “unknown exploits,” adding: “These kinds of exploits are particularly dangerous because a user’s security can be breached even when using fully updated software.”
What’d we miss? Email us to contribute — stephen@technical.ly (Baltimore) or michelai@technical.ly (D.C.).

This editorial article is a part of Technical.ly's Growing Industries month, when Technical.ly Baltimore is focusing extra reporting on the topic of cybersecurity.
Join our growing Slack community
Join 5,000 tech professionals and entrepreneurs in our community Slack today!
Donate to the Journalism Fund
Your support powers our independent journalism. Unlike most business-media outlets, we don’t have a paywall. Instead, we count on your personal and organizational contributions.

A founder’s vision comes alive at a showcase for Baltimore’s student entrepreneurs

Traditional PPE isn’t made for everyone. Here’s how one startup is fixing it.

Comcast introduces ultra-low lag Xfinity internet that boosts experiences with Meta, NVIDIA and Valve