You’ve gotten those extended car warranty calls, right? Or perhaps an email alerting you of suspicious activity on your bank card? These are classic examples of social engineering.
They happen every day and can take many different forms. Sadly, many people fall for them and lose substantial amounts of their personal money. Businesses aren’t immune, either: Nearly 70% of US organizations experienced social engineering in 2017, resulting in a $2.76 million loss.
So if cybercriminals are increasingly using social engineering in their cyberattacks, how are we training the next-generation workforce about it?
What is social engineering?
Social engineering is a tactic that uses psychological persuasion techniques to manipulate human beings to do or disclose something. On its own, social engineering isn’t malicious. In fact, we’ve probably all used it in our day-to-day activities — say, children convincing their parents to get a sugary snack, or students persuading their teachers for an extension.
However, social engineering can be used maliciously using psychological persuasion strategies, such as fear (suspicious activity on your card — log in into a replica bank website that is malicious), scarcity (limited time offers — click now!) or authority (your IT representative needs your username and password to clean your computer remotely).
Social engineering in the classroom
I’ve been teaching at Temple University in Philadelphia for 10 years now and I’ve repeatedly heard liberal arts and other non-technical students say, “We can’t do cyber because we don’t know how to code or hack.” I find this problematic, because the message we are giving the next generation is that if you lack technical skills, there is no room for you in cyber.

Aunshul Rege. (Courtesy)
I think this is also compounded by what is being recognized and celebrated as “cybersecurity.” For instance, there is a heavy investment in technical cybersecurity education programs, certificates and competitions. And this is unquestionably important. But cyber is more than just technical; it is inherently social. I typically respond to my students with, “So you don’t know how to code, but you know how people think. You can research how cybercriminals think, function in groups, and adapt.”
These are just as important as technical skills. If you don’t understand the adversary, how can you defend?
As an educator, I needed to get this point across. I had to force myself to move outside of my comfort zone and think about how to practice experiential learning in my classroom. If computer science students can try ethical hacking as part of their classroom experience, what can I do for the liberal arts students?
Since 2017, students in my cybercrime class have tried an assortment of projects, such as shoulder surfing; pretexting; privacy, terms and conditions; phishing; vishing; and open-source intelligence (OSINT). Every semester, I tweaked the projects based on student feedback, improved my rubrics, and realized that experiential cybersecurity education with a social science focus is possible and enjoyable! And I wanted to help other educators out, so I posted these projects on my lab’s website for other teachers to use for free.
Developing academic-industry-government-nonprofit partnerships
When I shared these projects and student experiences at various education and cybersecurity conferences, I was often approached by students at other institutions who wished they could also learn about social engineering. I wondered if I could scale these projects from my classroom to a larger platform. But I couldn’t do it alone. I reached out to the Layer8 conference, a nonprofit, and they agreed to partner with my lab.
We hosted our first CollegiateSECTF in October 2020, which was funded by the National Science Foundation. We had six professional social engineers who posed as judges and engaged with the six undergraduate student teams. In summer 2021, we hosted our SE Pen Testing competition. In addition to being funded by the National Science Foundation, I’m happy to share that the event was financially sponsored by Google and DUO Security. Representatives from CISA, MITRE ATT&CK and Google all engaged with the student teams from high school, undergraduate and graduate programs across the country and abroad. More recently, our competitions were included as a NICE Framework Success Story by the National Institute of Standards and Technology.

2021 Social Engineering Pen Testing Competition winners. (Courtesy image)
The government, industry and nonprofit representatives brought their expertise, real-world experiences, and enthusiasm to the event and stimulated student engagement. The financial support was fantastic, of course — 100% of the sponsor funds went to the students as prize money — but for me, the bigger win was the validation. I had industry, government and nonprofits all say that social engineering in cybersecurity education mattered, and they invested their time, expertise and money to prove it.
In just five years, I was able to move beyond projects in my classroom to (inter)national competitions. I developed collaborations with industry, government and nonprofits, all of whom saw value in teaching students about social engineering.
Educators need to think outside the box and be open and brave to try new things. If we are responsible for training the next generation workforce, we must bring innovation into our educational and training practices.
Students want to learn about social engineering
Many of the students who participated in the Summer Social Engineering event and the CollegiateSECTFs said their current cybersecurity curriculums didn’t train them in social engineering, and area they thought was increasingly being exploited in cyberattacks. They saw this as relevant to their cybersecurity training.
We opened up our 2021 summer social engineering event to high school and graduate students as well, many of whom were eager to participate. One team stated that the competitions they engaged in focused mainly on networking, which meant the event was a great way for them to experience the human side of cybersecurity “in a safe, fun, and engaging way.” Another team said the competition gave them exposure “to another aspect of cybersecurity that is not normally covered in the classes or in most workplaces.”

The first-place winners of the 2021 CollegiateSECTF was Temple University’s team, The Shoulder Surfers (L to R): Harrison Fedor, Ryan Harding, Aaron Scofield and Dane Gilmer. (Courtesy photo)
Being inclusive of all disciplines to promote diversity in thinking about cybersecurity
Unlike technical cybersecurity competitions (and there are many) that cater exclusively to computer science and engineering students, the social engineering competitions we host via the CARE Lab are open to students from ALL disciplines. I want all disciplines to feel welcomed and valued for their unique perspectives and skills; I want them to realize that they belong and can contribute to cybersecurity.
And what better way to demonstrate this by looking behind the scenes? The competition organizers at the Temple CARE Lab are all women who specialize in the social sciences.
My takeaway: Cybersecurity is for everyone and we all have to do our part to develop holistic and effective solutions that cater to an ever-changing threat landscape.
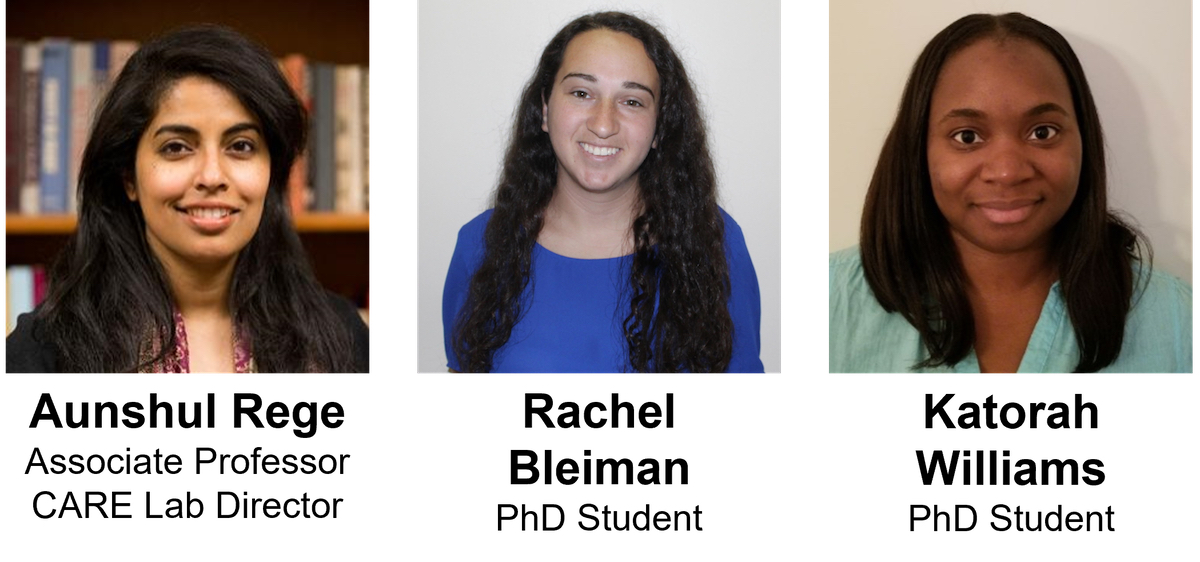
The CARE Lab team: Director Dr. Aunshul Rege and Ph.D. students Rachel Bleiman and Katorah Williams. (Courtesy image)
Join the conversation!
Find news, events, jobs and people who share your interests on Technical.ly's open community Slack

Philly daily roundup: Women's health startup wins pitch; $204M for internet access; 'GamingWalls' for sports venues

Delaware daily roundup: Delmarva Power vendor stats; DelDOT's $15M federal grant; 50 best companies to work for

DC daily roundup: Inside UMCP's new ethical AI project; HBCU founder excellence; a big VC shutters MoCo office

