On the afternoon of April 27, James Foster, CEO of Federal Hill-based cybersecurity company ZeroFOX, sent an email to a group of city leaders. The subject was marked “IMMEDIATE CALL TO ACTION.”
“We are trying to get in touch with the Mayor or Police Chief in Baltimore City asap as we turned on our system for Baltimore City and have some immediate intelligence for them,” Foster wrote, adding that the company recently provided similar services during protests in New York City.
Within the hour, he was connected with city and state officials, emails from city officials show.
An emailed report dated April 28 at 2:32 p.m. shows the information Foster discussed. It appears in a “Crisis Management” report that Foster said the company performed entirely for free in an effort to help the city amid the riots that followed Freddie Gray’s funeral.
“We worked around the clock,” he said, adding that employees, many of whom are Baltimore City residents, volunteered to work long hours to help.
ZeroFOX, which makes software that monitors social media accounts and other internet channels for potential cybersecurity threats, provided the 22-page report that looks at Twitter accounts, potential cyberattacks and makes recommendations for securing information.
On the fourth page, the report says ZeroFOX recorded 19 “threats mitigated,” and tallies up 340 real and fake social media accounts monitored.
But since the report was released via crowdfunded public records request, most of the focus has been on a few of those accounts.
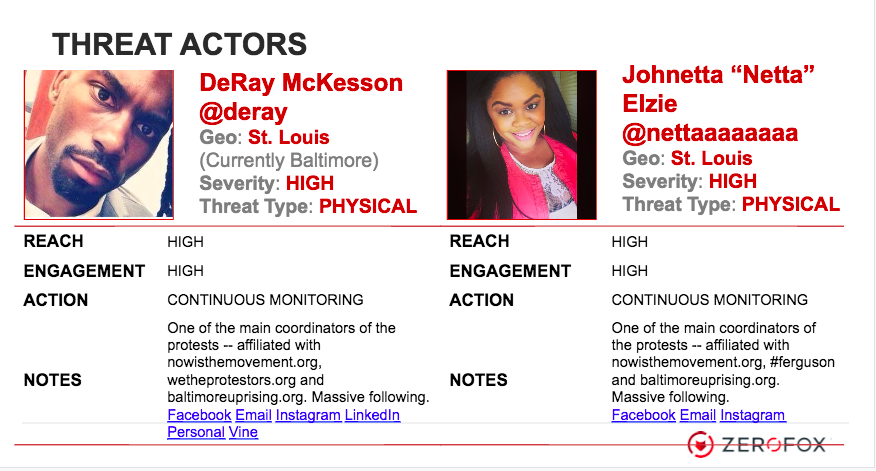
A section identifying “Threat Actors” includes information about national #BlackLivesMatter protest leaders DeRay McKesson (who is originally from Baltimore) and Johnetta Elzie, who have been called leaders of a 21st century civil rights movement.
Local grassroots collective Baltimore Bloc, which participates in events like the weekly West Wednesday that peacefully calls for justice in the case of Tyrone West, was also flagged. All three, who use Twitter as a means of organizing and advocating against police brutality, are labelled “Threat Type: Physical.”
The report, which wasn’t flagged in initial media reports about the emails, touched off a lengthy thread full of criticism on the Baltimore Tech Facebook page that currently has 256 comments (and counting). Stories followed Monday in national news outlets, including The Independent and Mother Jones.
Responding to a request for comment from the Baltimore Sun, McKesson tweeted:
@iduncan @Nettaaaaaaaa It is a reminder that the truth has always been a threat to a corrupt gov't apparatus.
— deray (@deray) July 29, 2015
In an interview with Technical.ly Baltimore, Foster and ZeroFOX cofounder Evan Blair said that despite the labels, the report wasn’t designed to be taken to mean that the protest leaders were out to do harm. ZeroFOX’s system likely identified the protest leaders due to the amount of followers they have on Twitter.
In part, the system identifies, “who are the biggest influencers out there, who are the people that have the biggest voices, the most reach,” and flags them for monitoring to keep track of the activities, Foster said.
“In any intelligence report, you would have to include two of the most well-known folks that are organizing activities,” Blair said. “If we didn’t include those two people, they would say didn’t understand two well-known people in the whole Baltimore protest.”
The ZeroFOX cofounders pointed out that the organizers were described as “main coordinators of the protests” in the report, without any specific malicious activity listed. Being labeled “physical,” they said, means the person is acting in real life rather than via cyber, Foster said.
The report advised that the city monitor the protest leaders. There was no indication that the company performed monitoring beyond the report. Foster said the information was passed to the city, and decisions on what to do with the info was up to officials.
City spokesman Howard Libit declined to comment on how the city used the information in the report, or even say if it was used. A separate email released by the city showed a spreadsheet of activities that were apparently being monitored by city officials. Two @deray tweets are listed, but it’s not clear how or why they were flagged.
North and Pennsylvania. Baltimore. https://t.co/yG1gA42C2k
— deray (@deray) April 27, 2015
At this point in time, it’s common for police to monitor social media during such events, said UMBC cybersecurity professor Richard Forno.
“It would surprise me if the Baltimore Police were not already monitoring social media as a part of law enforcement duties,” Forno said. Since they are in charge of public safety, police “can and should” use tools at their disposal to keep rights of way, and check for violence, Forno said.
ACLU attorney Nusrat Jahan Choudhury pointed out that government monitoring of protesters is not new. She recalled how civil rights leaders like Martin Luther King, Jr. and others were later found to be monitored by the FBI. But the information gathered has the potential to be kept beyond the march, she said.
“Government surveillance can lead to activity reports. Reports can be shared with law enforcement. The connection is that the surveillance can lead police to track or look further into people” just because they attended a protest, Choudhury said.
ZeroFOX’s Foster and Blair said that some of the Twitter accounts the company’s software identified were found to be malicious, whether fraud accounts posing as the Baltimore Police Department or officials like Mayor Stephanie Rawlings-Blake.
“We saw attacks from Russia pretending to be protesters inciting violence,” Foster said. “There are foreign governments that just want to see chaos.” (For more on that, check out this great Adrian Chen piece.)
Other accounts spread malware through pictures that purported to be from the riots, Foster said.
The report also warned that there was evidence of cyberattacks on four different city servers, and projected that another wave would hit around 3-5 p.m. on April 28. Libit, the city spokesman, confirmed the city faced “a number of different cyber attacks — and threats of cyber attacks.”
“There was also a period of time when portions of the city’s website were offline due to what is commonly referred to as denial of service attacks — something that was reported by other media outlets at the time,” Libit said in an email. “This was for a period of roughly 16 to 20 hours.”
He declined to comment on whether ZeroFOX’s report was a factor in the city’s recognition of the cyberattacks.
Forno, the UMBC professor, said such attacks are often a part of civil unrest. He said cities should be prepared, as legitimate forms of communication could be at risk.
“Fortunately, we believe that the city’s email system and internal core functions were unaffected throughout,” Libit said.
ZeroFOX’s report makes a number of recommendations. At one point, it advises officials to tell Gov. Larry Hogan that his social and email addresses may have been compromised.
Another advises the city to migrate services to the cloud, or get programs like CloudFlare or Akamai that “mitigate” denial of service attacks. When asked about accusations that the company was seeking business from the government during a crisis, Foster said ZeroFOX doesn’t sell those kinds of services.
“We recommended five other security products in the report that they should buy,” he said. “That to me is the worst sales pitch I’ve ever heard of.”
Baltimore City is not a client of ZeroFOX, Foster said.
Before you go...
Please consider supporting Technical.ly to keep our independent journalism strong. Unlike most business-focused media outlets, we don’t have a paywall. Instead, we count on your personal and organizational support.
Join our growing Slack community
Join 5,000 tech professionals and entrepreneurs in our community Slack today!

The person charged in the UnitedHealthcare CEO shooting had a ton of tech connections

From rejection to innovation: How I built a tool to beat AI hiring algorithms at their own game

Where are the country’s most vibrant tech and startup communities?